HIBP Domain Search.
Have I Been Pwned is a great resource for tech and non-tech folks alike. In fact it’s generally the first resource I point friends and family to when trying to help them understand why the use of common passwords is a security sin!
You may be aware that Troy Hunt expanded his awesome platform to allow IT Admins the ability to perform searches for pwned accounts falling under the umbrella of their company domain.
Setup is really simple and, as you’d imagine, the first and only stage is to prove that you own the domain in question.
To do this head along to the HIBP Domain Search page and enter your domain name.
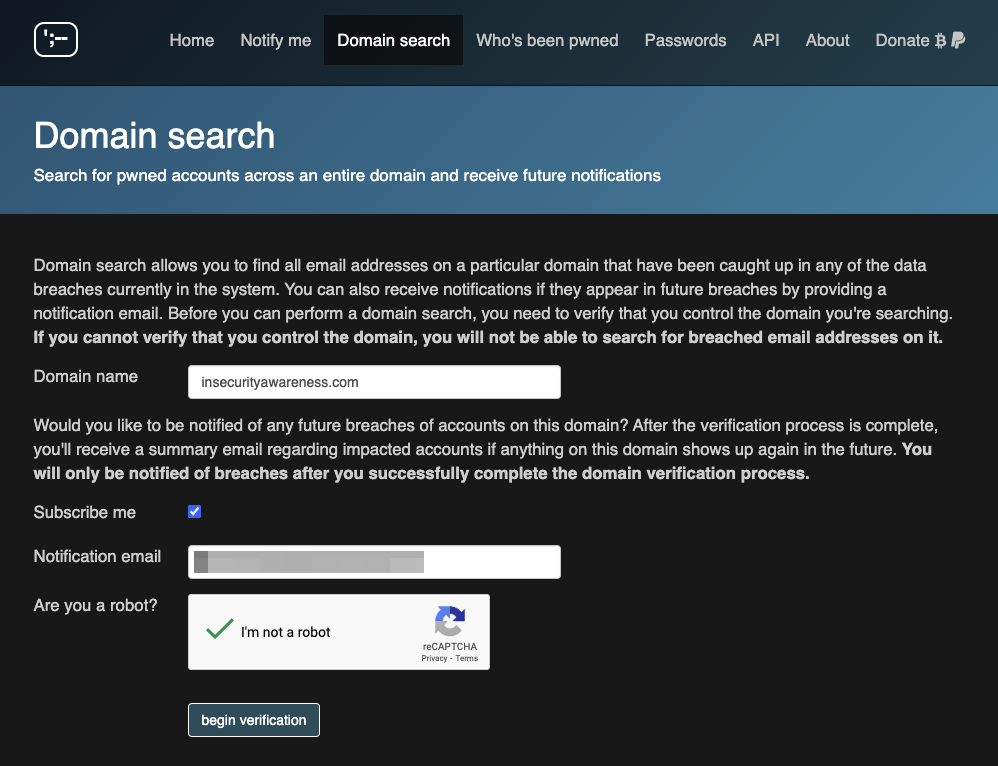
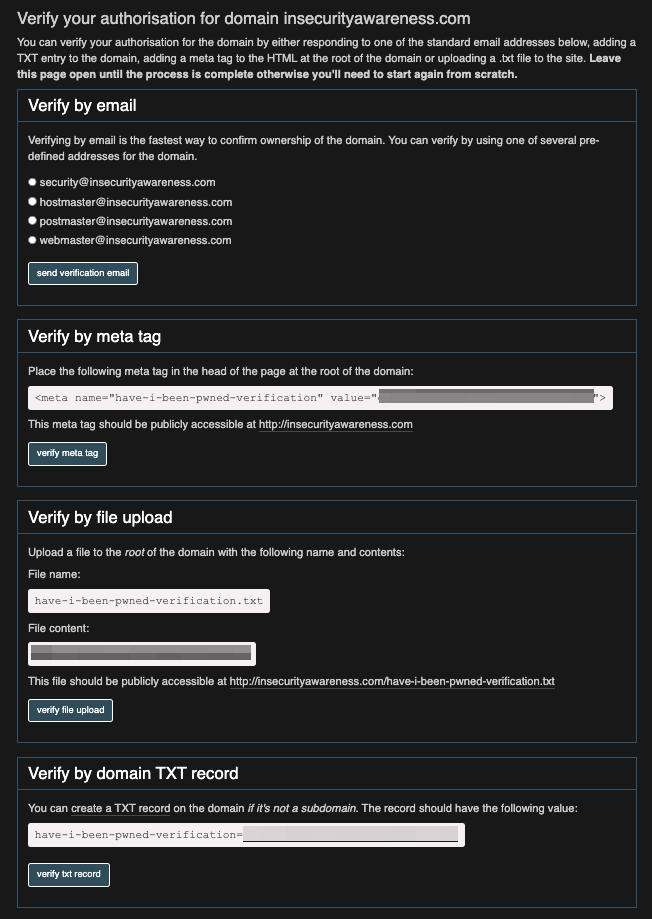
It’s then time to prove you own and have control over the specified domain. Verification can be achieved by completing one of four options;
- Email (use one of the supplied email addresses)
- Meta tag (add to the heading of the page on the root domain)
- File upload (upload a file with the supplied filename and content to the root of the domain)
- Create a DNS TXT record
Once verified, that’s it, you’re setup and the data can be downloaded in a few different formats. Simple eh!
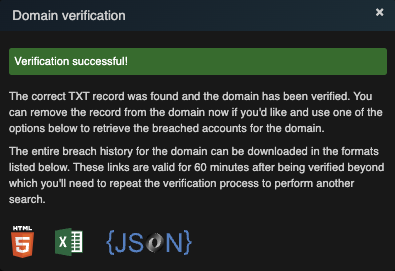
Assuming you previously entered an email address, you should now be notified of breaches that include addresses from your domain. This not only allows you to act immediately to protect your assets, but also provides a great opportunity to help your staff understand and tackle the cyber risks that we’re becoming accustomed to in modern day life.
- Hashcatalyst: Automating password cracking
- Kerberoasting Under Fire: How Group Managed Service Accounts Can Save the Day
- From Shadows to Signals: Hunting Pass-the-Hash Attacks
- NTLM is (finally) Dying
- From File Deletion to Domination: Exploiting Cisco’s VPN Clients for Privilege Escalation
About In.security.
In.security was formed by Will and Owen, two cyber security specialists driven to help other organisations stay safe and secure against cyber threats and attacks. After having worked together since 2011 in several former companies, they each gained considerable experience in system/network administration, digital forensics, penetration testing plus training. Based in Cambridgeshire, but operating nationally, we can provide a range of services and training for businesses and individuals alike. Read more about our services below:
- Penetration testing
- Vulnerability assessments
- Build reviews
- Red team testing
- Phishing assessments
- Password auditing
- Cloud security auditing